Course Details
Your Growth, Our Mission
Course Description
The Proxy SG v6.6 Advanced Administration course is intended for IT professionals who wish to learn to master the advanced features of Proxy SG.
The Training Course Will Highlight ?
Training Objective
- Solve common authentication and SSL issues
- Understand the underlying architecture of SGOS
- Monitor and analyze Proxy SG performance
- Use policy tracing as a troubleshooting tool
Target Audience
This course is for IT network or security professionals who have practical experience with the Proxy SG in the field and wish to master the advanced network security of Proxy SG.
Training Methods
Daily Agenda
Module 1: Using Authentication Realms
- Describe the benefits of enabling authentication on the Proxy SG
- Describe, at a high level, the Proxy SG authentication architecture
- Understand the use of IWA realms, with both IWA Direct and IWA BCAAA connection methods
Module 2: Understanding Authentication Credentials
- Describe how NTLM and Kerberos authentication work in both IWA direct and IWA BCAAA deployments
- Configure the Proxy SG to use Kerberos authentication
Module 3: Understanding Authentication Modes
- Describe authentication surrogates and authentication modes
- Describe Proxy SG authentication in both explicit and transparent deployment mode
Module 4: Understanding HTTPS
- Describe key components of SSL encryption
- Describe how the SSL handshake works
- Describe some of the legal and security considerations related to use of the SSL proxy
Module 5: Managing SSL Traffic on the Proxy SG
- Describe how the SSL proxy service handles SSL traffic
- Describe the standard keyrings that are installed by default on the Proxy SG
- Identify the types of security certificates that the Proxy SG uses
Module 6: Optimizing SSL Interception Performance
- Configure the Proxy SG to process SSL traffic according to best practices for performance
Module 7: SGOS Architecture
- Identify key components of SGOS
- Explain the interaction among client workers and software workers in processing client requests
- Explain the significance of policy checkpoints
- Describe key characteristics of the SGOS storage subsystem
- Explain the caching behavior of the Proxy SG
Module 8: Caching Architecture
- Describe the benefits of object caching on the Proxy SG
- Explain the caching-related steps in a Proxy SG transaction
- Identify and describe the HTTP request and response headers related to caching
- Describe, in general terms, how the Proxy SG validates cached objects to ensure freshness
- Explain how the Proxy SG uses cost-based deletion, popularity contests, and pipelining to improve object caching
Module 9: System Diagnostics
- Describe the use of the health monitor and health checks
- Explain the use of the event and access logs
- Describe the information available in advanced URLs and sys info files
- Describe the function of policy tracing and packet captures
Module 10: Introduction to Content Policy Language (CPL)
- Describe the fundamental concepts and purposes of Proxy SG policy transactions
- Understand the relationship of layers, rules, conditions, properties, and triggers
- Describe the two types of actions in CPL
- Describe how to write, edit, and upload CPL code
Module 11: Using Policy Tracing for Troubleshooting
- Identify the two main types of Proxy SG policy traces
- Describe the various sections of a policy trace result
- Configure a global and policy-driven trace
- Access and interpret policy trace results
Module 12: Proxy SG Integration
- Identify other Symantec products that can be used as part of a complete security solution
Accreditation
Quick Enquiry
Request Info
Course Rounds
2 Days| Code | Date | Venue | Fees | Action |
|---|
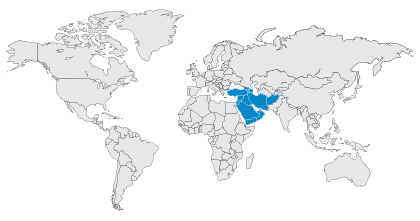
Prices don't include VAT
Related Courses
Your Growth, Our Mission

