Course Details
Your Growth, Our Mission
Course Description
The Training Course Will Highlight ?
Training Objective
- Offensive and defensive security strategies and approaches
- Implement security in layers ranging from physical security, network security, and operating system security
- Secure authentication, access-control on file systems, and password policies for users
- Use Network Access Protection (NAP), firewalls, and protocol security for data in-flight
- Use security software as counter-measures, including anti-virus software, anti-spam software, and encryption
Target Audience
IT management, project managers, compliance personnel, business analysts, or anyone who requires a basic understanding of core security concepts and their application in a private or public sector setting.
Training Methods
Daily Agenda
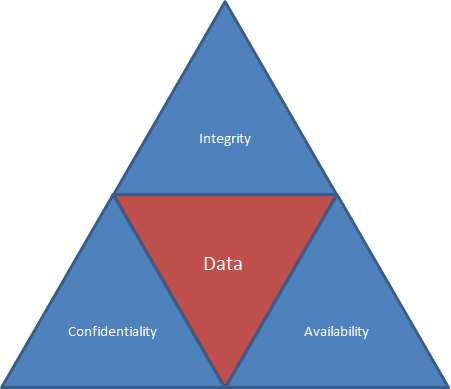
Security Layers
Security Fundamentals
Physical Security as the First Line of Defense
Core Security Principles
Physical Security
Authentication, Authorization, and Accounting
Authentication
Rights and Permissions
Auditing
Encryption
User Authentication
Audit Policies
Security Policies
Using Password Policies to Enhance Security
Network Security
Using Dedicated Firewalls to Protect a Network
Controlling Access with Network Access Protection (NAP)
Using Isolation to Protect the Network
Protecting Data with Protocol Security
Securing a Wireless Network
Network Isolation
Protocol Security
Wireless Security
Protecting the Server and Client
Protecting a Computer from Malware
Protecting the Client Computer
Protecting E-Mail
Protecting a Server
Securing Internet Explorer
Accreditation
Quick Enquiry
Request Info
Course Rounds
3 Days| Code | Date | Venue | Fees | Action |
|---|
Prices don't include VAT
Related Courses
Your Growth, Our Mission

